11. Configuration » Components » Flow Sensor¶
Many routers and switches can collect IP traffic statistics and periodically export them in form of flow records to Flow Sensor. Since the flow protocol already performs pre-aggregation of traffic data, the flow data sent to Flow Sensor is much smaller than the monitored traffic, and this makes the Flow Sensor a good option for monitoring remote or high-traffic networks. The advantages and disadvantages of flow-based monitoring are listed in the Choosing a Method of Traffic Monitoring and DDoS Detection section.
For detailed instructions on how to enable NetFlow, sFlow or IPFIX on your network device, please consult its documentation. Appendix 2 lists some configuration examples for a few Cisco IOS, CatOS, and Juniper devices.
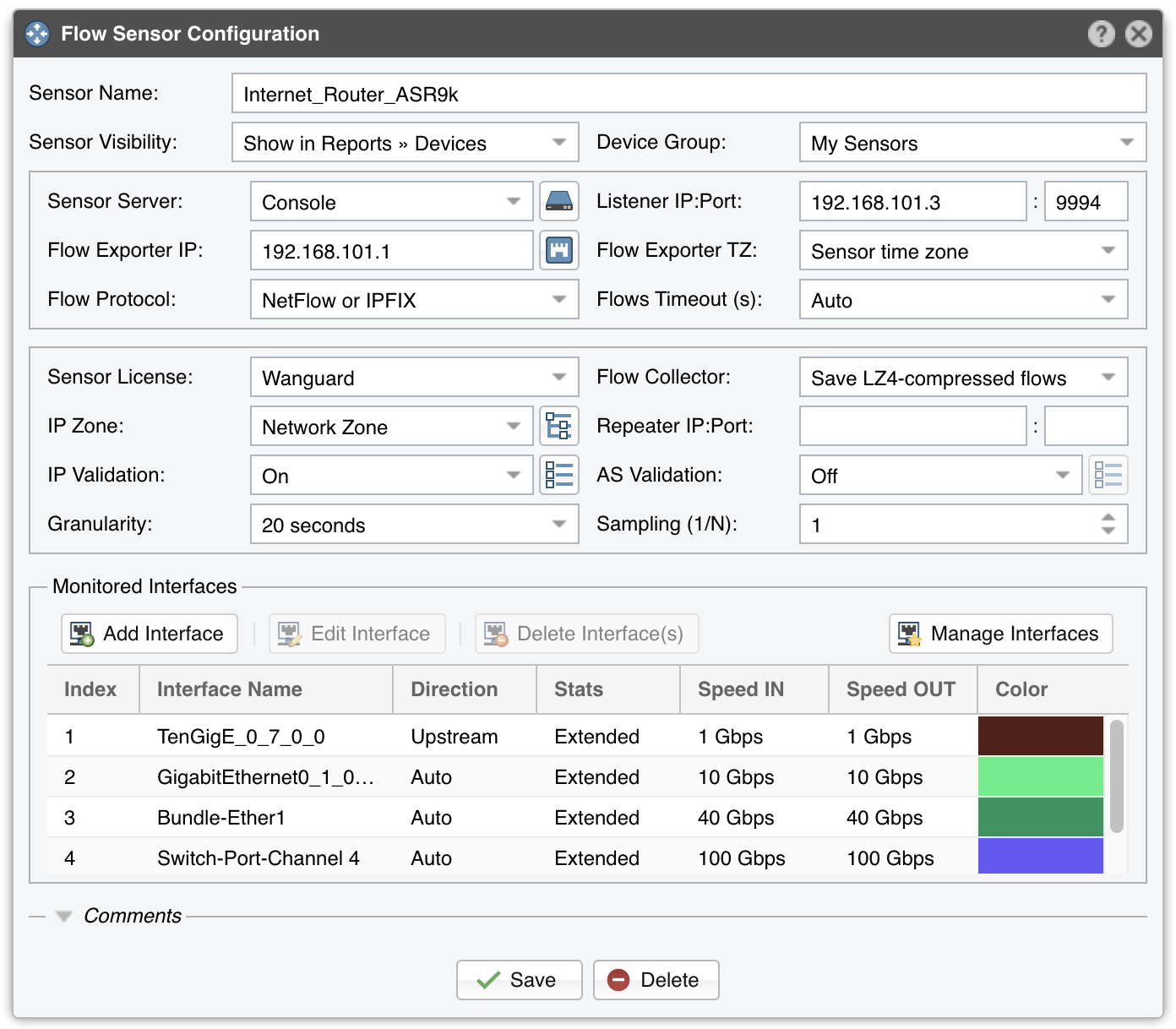
To add a Flow Sensor, click the [+] button from the title bar of the Configuration » Components panel. To modify an existing Flow Sensor, go to Configuration » Components and click its name.
● Sensor Name – A short name to help you identify the Flow Sensor● Reports Visibility – Toggles the visibility inside Reports » Devices● Device Group – Optional description used used to group up components (e.g. by location or role). It can be used to restrict the access of Guest accounts● Sensor Server – The server that runs the Flow Sensor. The configuration of servers is described in the Configuration » Servers chapter. If this is not the Console server, follow NFS configuration for remote servers to make the raw flow data visible in the UI● Listener IP:Port – The IP address (IPv4 or IPv6) of the network interface that receives the flow packets, and the destination port● Flow Exporter IP – IP address of the flow exporter (router, switch, probe). Usually, it is the loopback address of the router. For sFlow exporters, enter the IP that sends flow packets, not the Agent IP● SNMP Settings – Click the button on the right side of the Flow Exporter IP field. You must enable SNMP on the flow exporter to allow Console to automatically extract interface information. When SNMP settings are not configured, you must manually enter the SNMP index, speed, etc. for each interface● Flow Exporter TZ – Set the time offset between the time zone (TZ) of the Flow Sensor server and the time zone of the flow exporter. Running NTP on both devices to keep their clocks synchronized is a critical requirement● Flow Protocol – Flow protocol used by the flow exporter: NetFlow, IPFIX or sFlow● Flows Timeout (s) – Some flow exporters (e.g. Juniper MX) maintain the start time of flows that were already exported. If this is the case then you need to set here the same flow active/inactive timeout value (in seconds) as the one defined in the flow exporter’s configuration● Sensor License – The license type allocated to the Flow Sensor. Wanguard provides all features; Wansight does not provide traffic anomaly detection and reaction● Flow Collector – When enabled, flow data is stored in a space-efficient binary format. LZO is the fastest. BZ2 offers the best compression rate but it’s 30 times slower than LZO. LZ4 offers a compromise between speed and efficiency. Flow records can be queried in Reports » Tools » Flows● IP Zone – Flow Sensor needs an IP Zone from which to learn the monitored network’s boundaries and to extract per-subnet settings. For more information about IP Zones consult the dedicated chapter: Configuration » Network & Policy » IP Zone● Repeater IP:Port – An embedded packet repeater can send all incoming flows to another flow collector or host. To use this optional feature enter the IP of the other flow collector and a port of your choice● IP Validation – This option can be used to distinguish the direction of traffic or to ignore certain flows:○ Off – Flow Sensor examines all flows and the traffic direction is established by the interface○ On – Flow Sensor examines the flows that have the source IP and/or the destination IP inside the selected IP Zone. This is the recommended setting for most setups○ Strict – Flow Sensor examines the flows that have either the source IP or the destination IP inside the IP Zone○ Exclusive – Flow Sensor examines the flows that have the destination IP inside the IP Zone● IP Validation Options – Set the Log Invalidated Flows field to Periodically if you want to see in the event log the percentage of invalidated flows and 10 flows failing validation, once every 10 ticks● AS Validation – Flows from BGP-enabled routers can contain the source and destination Autonomous System number (ASN). In most configurations if the AS number is set to 0 then the IP address belongs to your network. This rarely-used option is used for establishing traffic direction. AS validation has three choices:○ Off – Disables AS validation○ On – Flow Sensor examines only the flows that have the source ASN and/or the destination ASN inside the local AS list (defined below)○ Strict – Flow Sensor examines only the flows that have either the source ASN or the destination ASN inside the local AS list (defined below)● AS Validation Options – When AS Validation is enabled, you can enter all your AS numbers (separated by space) into the Local AS List field. Set the Log Invalidated Flows field to Periodically if you want to see in the event log the percentage of invalidated flows and 10 flows failing validation, once every 10 ticks● Granularity – Low values increase the accuracy of Sensor graphs, at the expense of increasing the RAM usage● Sampling (1/N) – Enter the sampling rate configured on the flow exporter, or “1” when no sampling rate is configured. For NetFlow v9 and sFlow the value entered here is ignored because the flow protocol automatically adjusts the sampling rate. To force a particular sampling value, enter it as a negative value● Monitored Interfaces – List of interfaces that should be monitored. To avoid producing duplicate flow entries, add only upstream interfaces○ SNMP Index – The interfaces are internally identifiable only by their SNMP indexes. Enter the index manually, or configure SNMP settings○ Interface Name – A short description used to identify the monitored interface. Descriptions longer than 10 characters clutter some reports○ Interface Color – The color used in graphs for the interface. The default color is a random one, which can be changed by clicking the drop-down menu○ Traffic Direction – Direction of traffic entering the interface, relative to your network:• “Auto” – When selected, the direction of traffic is established by IP and/or AS Validation alone. This is the recommended setting in most cases• “Upstream” – Set for upstream interfaces, e.g. peering interfaces, interfaces connected to the Internet• “Downstream” – Set for downstream interfaces, e.g. customer interfaces, interfaces connected to your network• “Null” – Traffic to Null interfaces is discarded by the router and should be ignored○ Stats Engine – Collects various traffic tops and AS (Autonomous System) data:• “Basic” – Enables tops for Internal IPs, IP protocols, versions and TCP/UDP ports. It adds a very small performance penalty• “Extended” (recommended) – Enables all tops from “Basic” as well as tops and graphs for autonomous systems and countries, but slightly increases the CPU usage. When the router does not export AS information in flows (e.g. non-BGP router), Flow Sensor uses an internal GeoIP database to obtain AS data. Live stats for autonomous systems and countries may not be very accurate• “Full” – Enables all tops from “Extended” as well as tops for external IPs (IPs not included in the IP Zone), but increases the RAM usage several times over, especially during spoofed attacks. Live stats for autonomous systems and countries are very accurate. Set the value to “Extended”, unless you know what you’re doing. Only this option permits the detection of threshold violations for external IPs○ Stats Engine Options – When Stats Engine is set to “Extended” or “Full”, you can click the button next to it. To enable Transit AS tops and graphs, enter the path to an existing BGP Dump File exported by BGPd in MTR format, and the IPv4 and optionally IPv6 address of the BGP router○ Link Speed In & Link Speed Out – Enter the speed (bandwidth, capacity) of the interface. The values are used for percentage-based reports and percentage-based bits/s thresholds● Comments – Comments about the Flow Sensor can be saved here. These observations are not visible elsewhere
To start the Flow Sensor, click the small button displayed next to its name in Configuration » Components. Ensure that the Flow Sensor starts correctly by watching the event log (details in the Configuration » Schedulers » Event Reporting section).
If the Flow Sensor starts without errors, but you can’t see any data collected by it in Reports » Devices » Overview after more than 5 minutes, follow the troubleshooting guide below.
11.1. Flow Sensor Troubleshooting¶
[root@localhost ~]# tcpdump -i <interface_eth0_p1p1_etc> -n -c 100 host <flow_exporter_ip> and udp and port <destination_port>
[root@localhost ~]# iptables -L -n -v && iptables -t raw -L -n -v
[root@localhost ~]# ntpq -p || chronyc tracking
set forwarding-options sampling instance NETFLOW family inet output inline-jflow flow-export-rate 40
set chassis fpc inline-services flow-table-size ipv4-flow-table-size 15