Reports » Tools » Firewall¶
Firewall tab lists the firewall rules managed by Wanguard, lists the filtering rules detected by Wanguard Filter, provides an easy way for Console users to add firewall rules, and generates statistics about filtering rules.
The term filtering rule is specific to Wanguard Filter and describes an attack pattern. Every filtering rule type is listed in General Settings » Anomaly Mitigation. Ideally, every filtering rule should be directly translatable into one or several firewall rules, but it depends on the type of firewall used. Netfilter supports all filtering rules, but other firewalls are more limited.
Active Firewall Rules¶
Shows a listing of active firewall rules that were generated automatically by Filters or introduced manually by Console users.
Administrators and operators can add firewall rules manually by clicking the [Add Firewall Rule] button and then by choosing one of the existing firewall options from the drop-down menu. The firewalls that are not defined in Filter configurations are hidden.
Create Netfilter Firewall Rule window parameters:
● Description – A short name that helps you identify the firewall rule. This is the only mandatory field● Filter(s) – Select the Filter that will apply your rule, considering its configuration (Filtering Interface, Netfilter Chain, Netfilter Table, etc.)● Direction – Select Inbound to match packets entering your network (through interfaces defined as Inbound in the Filter configuration). Otherwise, select Outbound● IP Protocol(s) – Select one or more IP protocols, or Any to match all packets● Source/Destination IP/mask – Enter to match packets by their source or destination IPs or subnets. The CIDR mask is optional, and values without it are considered hosts (mask defaults to /32 for IPv4 and /128 for IPv6)● Source/Destination Port(s) – This field is editable only for the following IP protocols: TCP, UDP, UDPLITE, DCCP, and SCTP. It matches a set of ports. You can specify up to 15 ports (e.g., 53, 1024:65535 would match ports 53 and all ports between 1024 and 65535)● IP Packet Length – It matches the length of the OSI Layer3 payload (e.g., Layer4 packet) against a specific value or range of values separated by “:”● IP TimeToLive – It matches the TTL field from the IP header. If the value is preceded by “>”, the packet is matched if TTL is greater than the given value. If the value is preceded by “<”, the packet is matched if TTL is less than the given value● TCP Flags Set/Unset – Select the TCP flags that must be explicitly set and/or unset. TCP flags that are not enabled in either field are ignored● Payload Content – Enter to match a string anywhere in the packet. Use this option with caution as it consumes a lot of CPU resources● Country(ies) – Select to match packets by their country of origin, but only if the xt_geoip Netfilter module is installed on the server● Firewall Policy – Select the Netfilter Firewall policy applied for the matched packets:• Drop – Block the packets• Reject – Block packets and sends an ICMP reply packet indicating that the port is unavailable• Accept – Allow packets to pass the firewall• Rate Limit – Allow a limited number of packets through the firewall● Rate Limit – You can use this parameter to limit the rate of packets per time unit to a predefined value. If the value ends with the character “b” then the rate-limiting is applied for bytes, not packets● Rate Limit Hashing – You can apply the rate-limiting globally, to a single object (Src. IP, Src. Port, Dst. IP or Dst. Port), or to any combination of objects. If the rate-limiting should be connection-oriented, select all objects. To rate-limit the packet or byte rate of each source IP, select the Src. IP object● Rule Active Until – Select Manually deleted to apply the firewall rule for an indefinite period. Select the other options to remove the firewall rule after a predefined condition
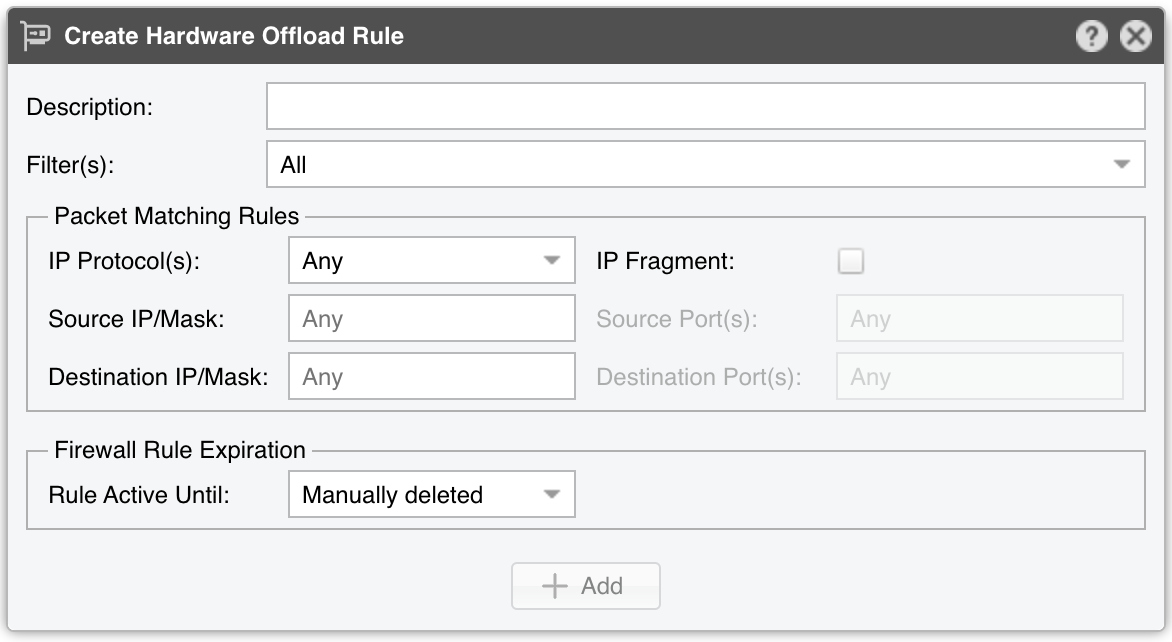
Create Hardware Offloading Rule window parameters:
● Description – A short name that helps you identify the rule. This is the only mandatory field● Filter(s) – Select the Filter that will apply your rule● IP Protocol(s) – Select one or more IP protocols, or Any to match all packets● IP Fragment – Select to match only fragmented packets● Source/Destination IP/mask – Enter to match packets by their source or destination IP blocks. The mask is optional, and values without it are considered hosts (mask defaults to /32 for IPv4 and /128 for IPv6)● Source/Destination Port(s) – This field is available only for the following IP protocols: TCP, UDP, UDPLITE, DCCP, and SCTP. It matches a set of source or destination ports● Rule Active Until – Select Manually deleted to apply the firewall rule for an indefinite period. Select the other options to remove the firewall rule after a predefined condition
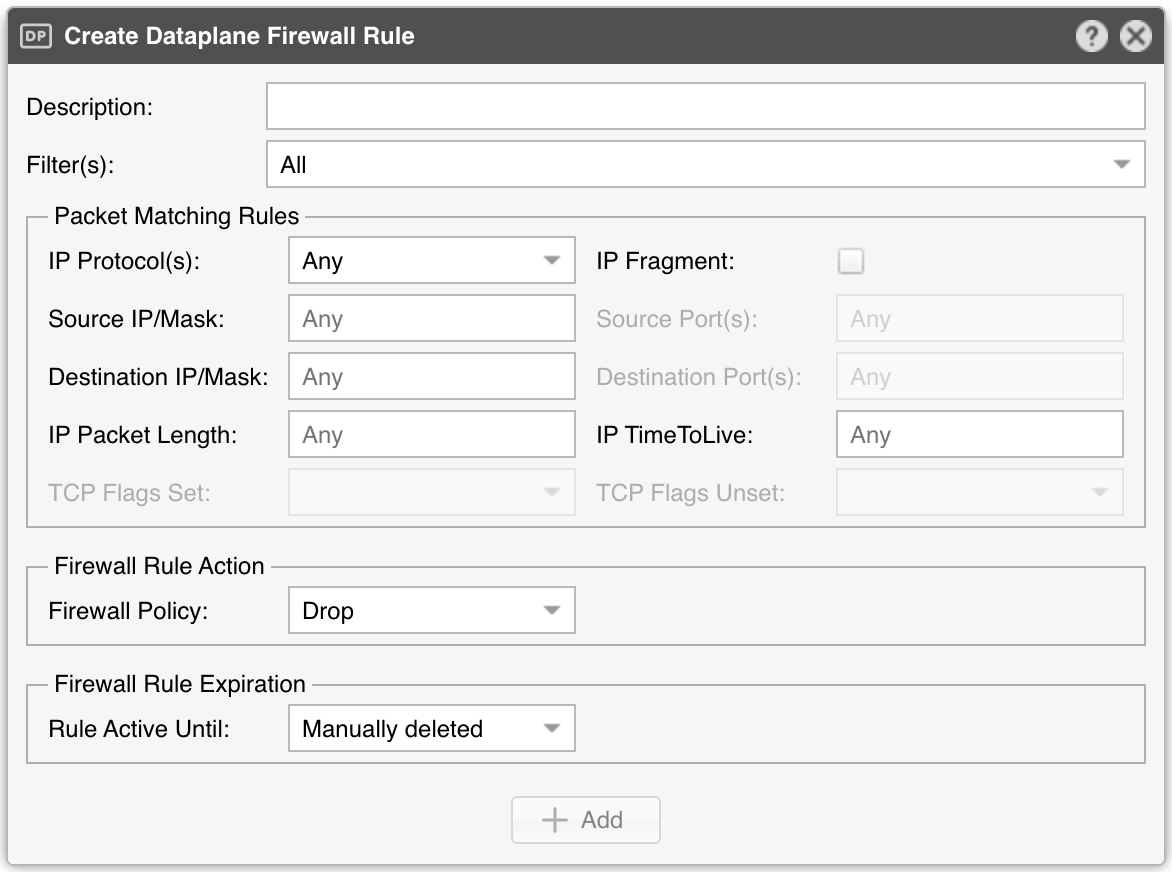
The Create Dataplane Firewall Rule window contains fields that were already described above.
When there is at least one active firewall rule, a table describing it is displayed in the content area. The matched counters are updated constantly. Some Firewall backends offer only partial counters (Chelsio) or no counters at all (Mellanox).
Filtering Rule Archive¶
Lists the filtering rules detected by the selected Filter(s) during the specified time range. Some columns are described in the Reports » Tools » Anomalies chapter.
Filtering Rule Distribution¶
Creates pie charts with filtering rule statistics.